Posts
-
Kubecon and CloudNativeCon 2024 Europe summary

This blog post shares my thoughts on attending Kubecon and CloudNativeCon 2024 Europe in Paris. It was my third time at this conference, and it felt bigger than last year’s in Amsterdam. Apparently it had an impact on public transport. I missed part of the opening keynote because of the extremely busy rush hour tram in Paris.
-
Back to the Wikimedia Foundation!
In October 2023, I departed from the Wikimedia Foundation, the non-profit organization behind well-known projects like Wikipedia and others, to join Spryker.
However, in January 2024 Spryker conducted a round of layoffs reportedly due to budget and business reasons. I was among those affected, being let go just three months after joining the company.
-
OpenTofu: handcrafted include-file mechanism with YAML

I recently started playing with Terraform/OpenTofu almost on a daily basis.
The other day I was working with Amazon Managed Prometheus (or AMP), and wanted to define prometheus alert rules on YAML files.
I decided that I needed a way to put the alerts on a bunch of files, and then load them by the declarative code, on the correct AMP workspace.
-
New job at Spryker

Last month, in October 2023, I started a new job as a Senior Site Reliability Engineer at the Germany-headquartered technology company Spryker. They are primarily focused on e-commerce and infrastructure businesses.
I joined this company with excitement and curiosity, as I would be working with a new technology stack: AWS and Terraform. I had not been directly exposed to them in the past, but I was aware of the vast industry impact of both.
Suddenly, things like PXE boot, NIC firmware, and Linux kernel upgrades are mostly AWS problems.
-
Wikimedia Hackathon 2023 Athens summary

During the weekend of 19-23 May 2023 I attended the Wikimedia hackathon 2023 in Athens, Greece. The event physically reunited folks interested in the more technological aspects of the Wikimedia movement in person for the first time since 2019. The scope of the hacking projects include (but was not limited to) tools, wikipedia bots, gadgets, server and network infrastructure, data and other technical systems.
My role in the event was two-fold: on one hand I was in the event because of my role as SRE in the Wikimedia Cloud Services team, where we provided very valuable services to the community, and I was expected to support the technical contributors of the movement that were around. Additionally, and because of that same role, I did some hacking myself too, which was specially augmented given I generally collaborate on a daily basis with some community members that were present in the hacking room.
-
Kubecon and CloudNativeCon 2023 Europe summary

This post serves as a report from my attendance to Kubecon and CloudNativeCon 2023 Europe that took place in Amsterdam in April 2023. It was my second time physically attending this conference, the first one was in Austin, Texas (USA) in 2017. I also attended once in a virtual fashion.
The content here is mostly generated for the sake of my own recollection and learnings, and is written from the notes I took during the event.
-
Debian and the adventure of the screen resolution

I read somewhere a nice meme about Linux: Do you want an operating system or do you want an adventure? I love it, because it is so true. What you are about to read is my adventure to set a usable screen resolution in a fresh Debian testing installation.
The context is that I have two different Lenovo Thinkpad laptops with 16” screen and nvidia graphic cards. They are both installed with the latest Debian testing. I use the closed-source nvidia drivers (they seem to work better than the nouveau module). The desktop manager and environment that I use is lightdm + XFCE4. The monitor native resolution in both machines is very high:
3840x2160(or4K UHDif you will). -
Home network refresh: 10G and IPv6

A few days ago, my home network got a refresh that resulted in the enablement of some next-generation technologies for me and my family. Well, next-generation or current-generation, depending on your point of view. Per the ISP standards in Spain (my country), what I’ll describe next is literally the most and latest you can get.
The post title spoiled it already. I have now 10G internet uplink and native IPv6 since I changed my ISP to https://digimobil.es.
-
New OpenPGP key and new email
I’m trying to replace my old OpenPGP key with a new one. The old key wasn’t compromised or lost or anything bad. Is still valid, but I plan to get rid of it soon. It was created in 2013.
The new key id fingerprint is:
AA66280D4EF0BFCC6BFC2104DA5ECB231C8F04C4I plan to use the new key for things like encrypted emails, uploads to the Debian archive, and more. Also, the new key includes an identity with a newer personal email address I plan to use soon: arturo.bg@arturo.bg
-
Netfilter Workshop 2022 summary

This is my report from the Netfilter Workshop 2022. The event was held on 2022-10-20/2022-10-21 in Seville, and the venue was the offices of Zevenet. We started on Thursday with Pablo Neira (head of the project) giving a short welcome / opening speech. The previous iteration of this event was in virtual fashion in 2020, two years ago. In the year 2021 we were unable to meet either in person or online.
This year, the number of participants was just eight people, and this allowed the setup to be a bit more informal. We had kind of an un-conference style meeting, in which whoever had something prepared just went ahead and opened a topic for debate.
-
Toolforge Jobs Framework
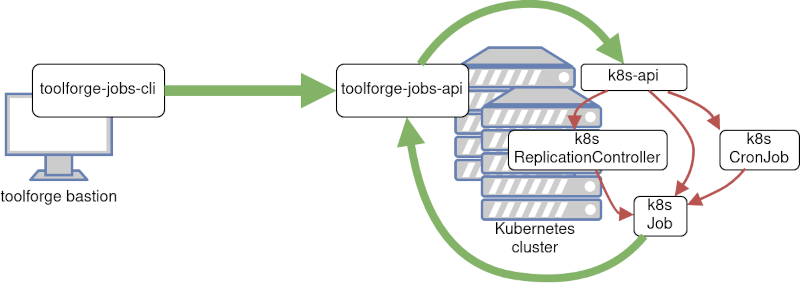
This post was originally published in the Wikimedia Tech blog, authored by Arturo Borrero Gonzalez.
This post continues the discussion of Toolforge updates as described in a previous post. Every non-trivial task performed in Toolforge (like executing a script or running a bot) should be dispatched to a job scheduling backend, which ensures that the job is run in a suitable place with sufficient resources.
-
Toolforge GridEngine Debian 10 Buster migration
This post was originally published in the Wikimedia Tech blog, authored by Arturo Borrero Gonzalez.
In accordance with our operating system upgrade policy, we should migrate our servers to Debian Buster.
As discussed in the previous post, one of the most important and successful services provided by the Wikimedia Cloud Services team at the Wikimedia Foundation is Toolforge. Toolforge is a platform that allows users and developers to run and use a variety of applications with the ultimate goal of helping the Wikimedia mission from the technical side.
-
Wikimedia Toolforge and Grid Engine

This post was originally published in the Wikimedia Tech blog, authored by Arturo Borrero Gonzalez.
One of the most important and successful products provided by the Wikimedia Cloud Services team at the Wikimedia Foundation is Toolforge, a hosting service commonly known in the industry as Platform as a Service (PaaS). In particular, it is a platform that allows users and developers to run and use a variety of applications with the ultimate goal of helping the Wikimedia mission from the technical side.
-
Iterating on how we do NFS at Wikimedia Cloud Services

This post was originally published in the Wikimedia Tech blog, authored by Arturo Borrero Gonzalez.
NFS is a central piece of infrastructure that is essential to services like Toolforge. Recently, the Cloud Services team at Wikimedia had been reviewing how we do NFS.
subscribe via RSS